Seokchan Yoon
ch4n3.yoon@gmail.com
About
Offensive Web Security Researcher
GitHub, GitLab, Python, Django, FastAPI(Starlette), Apache Airflow, Ruby, Ruby on Rails, Java Spring 보안 기여자
DEF CON 33 CTF 결선 진출: 2016년부터 활동 중인 CTF 경쟁자(약 10년)
수상: 국방부 장관 표창(2024), 국가보안기술연구소장 표창(2022, 2021), 사이버작전사령관 표창(2019), 교육부 장관상(2018)
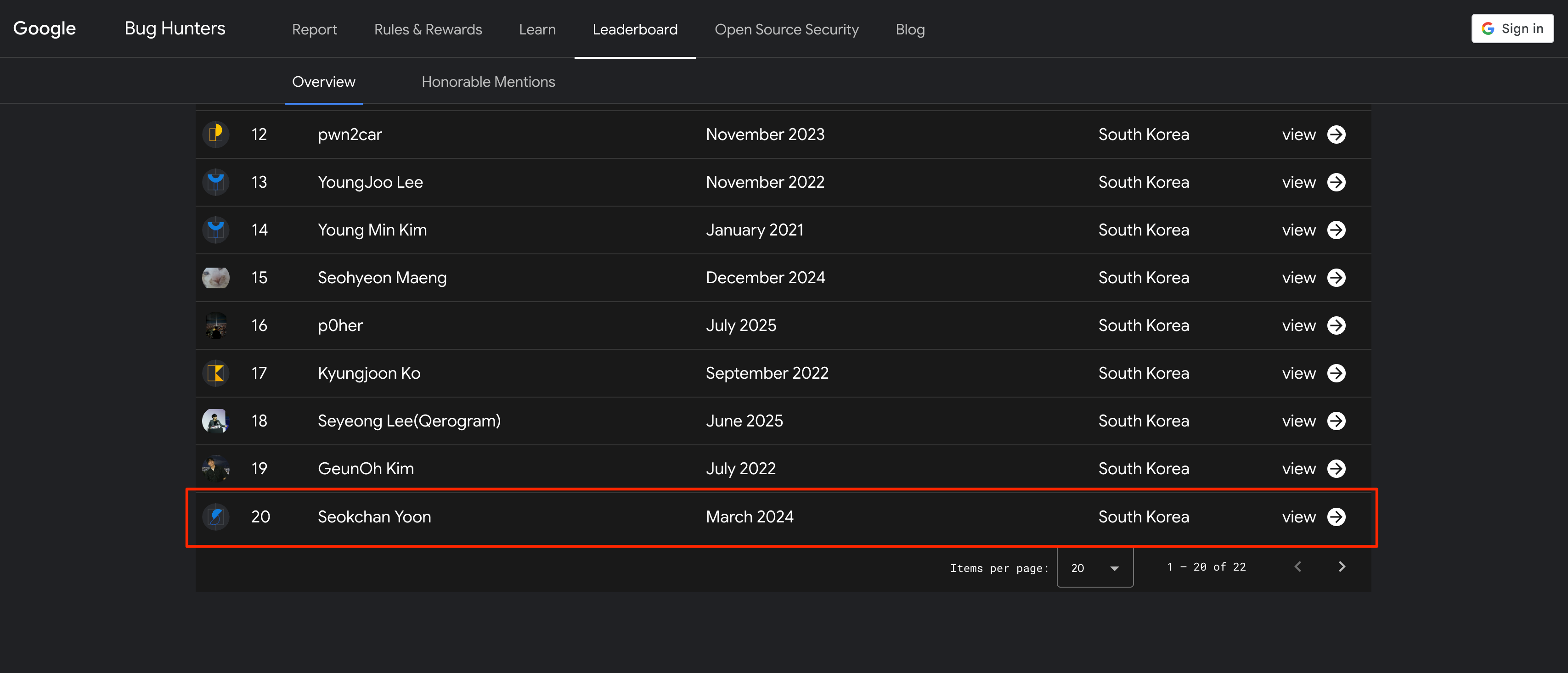
Google, Naver 버그 바운티 명예의 전당 등재
Work Experience
Zellic.io
USA - remote
Security Researcher
Apr. 2025 - now
Web2 Infrastructure & Application Auditing
Conducted comprehensive security assessments on complex Web2 architectures, ranging from SaaS platforms to crypto-exchange infrastructures.
Performed manual source code review and grey-box testing to identify potential vulnerabilities (e.g., SQL Injection, Business Logic Flaws, Denial-of-service)
Security Consulting & Risk Management
Collaborated directly with clients to define practical remediation strategies.
Advised on security trade-offs, balancing robust defense mechanisms with product usability and business operational requirements.
Airflow Security Team, Apache Software Foundation
USA - remote
Security Team Member
Jul. 2025 - Jan. 2026
Reviewing and addressing security vulnerabilities in Apache Airflow
Collaborating with the open-source community
Maintaining the security posture of the project in accordance with ASF guidelines
PWNLAB (System Security Lab), Kyung Hee University
S.Korea
Undergraduate Research Intern
Mar. 2025 - Jan. 2026
Developed a multi-cloud security audit tool for Samsung Electronics to automate compliance checks across AWS, GCP, and Azure
Implemented 260+ security inspection checks (IAM, Network, Container, Database, Storage, Monitoring, Logging) using Python and FastAPI, aligned with IaC principles
Engineered an agentless, multi-threaded scanning engine optimized for large-scale enterprise environments
Conducted black-box penetration testing on 19+ Samsung corporate web services; identified 10 vulnerabilities
Found several medium-impact issues including IDOR, file upload bypass, and reflected XSS
Advisor: Prof. Daehee Jang
[REDACTED] Institute under the Ministry of National Defense
S.Korea
Unit [REDACTED], Private [REDACTED]
Sep. 2023 - Mar. 2025
- Conducted research and development on [REDACTED]
STEALIEN
S.Korea
R&D / Proactive Response Team, Security Researcher
Jul. 2020 - Jun. 2023
Web Penetration Testing / Red Teaming
Conducted numerous penetration tests over 3 years targeting web services across major industries including finance, enterprises, and government agencies
Performed black-box assessments on diverse environments such as KB Kookmin Bank, Hana Bank, Ministry of Culture, Sports and Tourism and Ministry of Foreign Affairs-affiliated services, and Lotte Castle IoT systems
Executed a penetration testing engagement for the City of Bandung, Indonesia web services
CTF Platform Development and Operation
Designed and developed a custom web-based CTF platform (Django + React)
Managed the full pipeline of distributing, collecting, and uploading challenges across ~20 problem setters
Operated on-site competitions including the Ministry of Education Cybersecurity Competition and Ko-World CTF at Dubai GITEX
Internal Security Infrastructure
Designed and built internal GitLab, tech blog, deployment systems, and internal network environment to prevent external leakage of exploits
Education
KyungHee University
S.Korea
Computer Science & Engineering
Mar. 2020 - Feb. 2026
Best of the Best 6th
S.Korea
Vulnerability Analysis Track
Jul. 2017 - May. 2018
Korea Digital Media High School
S.Korea
Department of Hacking Defense
Mar. 2017 - Feb. 2020
Skills
Web Security & Vulnerability Research
- Web penetration testing
- Red-teaming
- Security auditing
- Vulnerability disclosure (CVE, HackerOne, Google VRP)
Development & Operations
- Educational system development (Cyber Drill System, Django + React)
- CTF competition operation
- Internal tools, technical blogs, deployment systems
Awards
2025 DEF CON CTF 33
Jan. 2025
2025 Cyber Conflict Exercise (CCE) General Division (사이버공격방어대회)
Korea
Jan. 2025
2024 White Hat Contest Soldier Division (화이트햇 콘테스트)
Korea
Awarded the Minister of National Defense Award
Jan. 2024
2023 CODEGATE University Division
Korea
Jan. 2023
2022 CODEGATE University Division
Korea
Jan. 2022
2022 Cyber Conflict Exercise (CCE) Public Institution Sector Division (사이버공격방어대회)
Korea
Awarded the Director of National Security Research Institute Award
Jan. 2022
2022 HACKTHEON SEJONG National University Cybersecurity Competition
Korea
Awarded the Director of National Security Research Institute Award
Jan. 2022
2021 Cyber Conflict Exercise (CCE) Public Institution Sector Division (사이버공격방어대회)
Korea
Awarded the Director of National Security Research Institute Award
Jan. 2021
2019 Cyber Operations Challenge Student Division (사이버작전경연대회)
Korea
Awarded the Cyber Operations Commander Award
Jan. 2019
2018 Cybersecurity Competition Individual Preliminary Round (정보보안경진대회)
Korea
Awarded the President of Seoul Women's University Award
Jan. 2018
2018 Cybersecurity Competition Team Finals (정보보안경진대회)
Korea
1st Place, hosted by the Ministry of Education, Korea
Awarded the Minister of Education Award
Jan. 2018
2017 Cybersecurity Competition Team Finals (정보보안경진대회)
Korea
Awarded the Director of Korea Education and Research Information Service Award
Jan. 2017
Open Source
CPython
- CVE-2024-7592: Denial of Service due to quadratic complexity parsing when handling cookies containing backslashes.
Django
CVE-2023-36053: Regular Expression Denial of Service in EmailValidator and URLValidator.
CVE-2024-24680: Denial of Service in the intcomma template filter.
CVE-2024-27351: Regular Expression Denial of Service in Truncator.words() function.
CVE-2024-21520: Cross-Site Scripting in Django Rest Framework's browsable API.
CVE-2024-41991: Denial of Service in urlize function and AdminURLFieldWidget.
CVE-2024-53908: SQL Injection in HasKey function when using Oracle databases.
CVE-2025-48432: Potential log injection via unescaped request path
CVE-2025-64458: Potential denial-of-service vulnerability in HttpResponseRedirect and HttpResponsePermanentRedirect on Windows
CVE-2025-64460: Potential denial-of-service vulnerability in XML serializer text extraction
CVE-2026-25673: Potential denial-of-service vulnerability in URLField via Unicode normalization on Windows
FastAPI / Starlette
CVE-2025-62727: O(n^2) DoS via Range header merging in starlette.responses.FileResponse
Apache Airflow
CVE-2024-39877: Code Execution vulnerability in the scheduler allowing DAG authors to execute arbitrary code
CVE-2024-39863: Potential Cross-Site Scripting in the web interface
CVE-2024-45034: Authenticated DAG authors can execute arbitrary code on scheduler nodes
CVE-2024-56373: Apache Airflow: SSTI to Code Execution in Airflow through Shared DB Information
Ruby
CVE-2024-41123: Denial of Service in REXML due to crafted XML inputs
Ruby on Rails
- CVE-2024-47887: Regular Expression Denial of Service in Action Controller's HTTP token authentication.
- CVE-2024-41128: Regular Expression Denial of Service in Action Dispatch's query parameter filtering.
Java Spring
- CVE-2024-38809: Denial of Service through crafted conditional HTTP requests.
GitHub
HackerOne#2646500: Pre-authenticated DoS Vulnerability in GitHub Enterprise
GitLab
HackerOne#3550632: OO disclosure via OO in gitlab.com (expected to receive CVE in March 2026)
Google VRP
Ranked at 20th in South Korea
Website